Reading time: 7m 35s
Your 12 words aren't going to cut it forever. That seed phrase you wrote down on a napkin (or hopefully something more durable) powers a thing called HD wallet - and the math keeping it safe is about to have a very bad decade.
Project Eleven just dropped a high-level research paper that tries to fix the problem before it becomes one.
We decided to break it down to save you the ache.
What are HD wallets?
If you've ever used Rabby, Ledger, Phantom, or pretty much any modern crypto wallet, you're already using a hierarchical deterministic (HD) wallet.
The concept comes from Bitcoin Improvement Proposal 32 (BIP32), introduced by Pieter Wuille in 2012, which solved a genuinely painful problem.

Before BIP32, wallets generated random key pairs every time you needed a new address.
Want a new receiving address? New random key. That means you'd need to back up your wallet after every single transaction or risk losing access to funds.
Imagine having to write down a new password every time you received a payment. Absolute nightmare.
BIP32 changed the game by introducing a tree-like structure where all your keys, every last one of them, are derived from a single master seed.
That seed becomes your 12 or 24 word recovery phrase. One backup. Done. Every key your wallet ever generates can be deterministically recreated from that seed, in the exact same order, every time.
But here's where it gets clever. BIP32 supports two key derivation modes: hardened and non-hardened.
Hardened derivation needs the parent private key to generate child keys. It's locked down, secure, and used for the top levels of your wallet's key tree (like account separation).
Non-hardened derivation is the magic trick. It lets you derive child public keys from a parent public key alone, without a private key.

This is what makes watch-only wallets possible. Your exchange, your accounting software, or a server generating fresh receiving addresses can all do their jobs without ever touching the signing key.
The private key stays offline, in the cold, exactly where it should be.
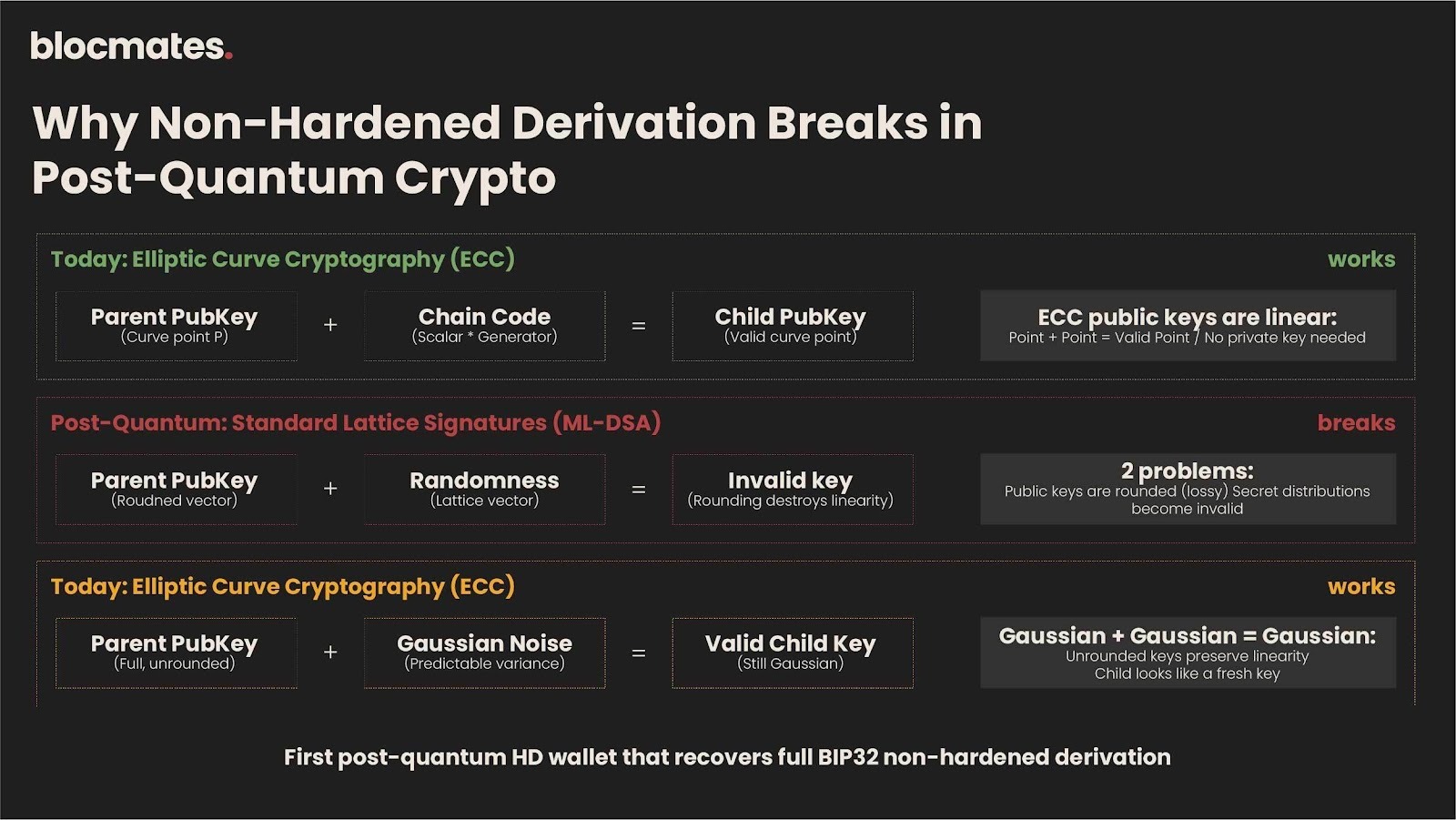
This whole system works because elliptic curve cryptography (ECC) has a neat algebraic property: you can add things to a public key and get another valid public key. It's linear. It's elegant. And it's the exact property that quantum computers are going to demolish.
The quantum problem nobody wants to talk about
We've all heard the "quantum computers will break crypto" line so many times that it's basically background noise at this point. But Project Eleven isn't just waving their arms about it - they've been putting actual numbers to the risk.
According to their Bitcoin Risq List, over 6.2 million BTC (BTC) currently sit in addresses with exposed public keys. That's hundreds of billions of dollars that would be vulnerable if a cryptographically relevant quantum computer (CRQC) were to appear tomorrow.
The threat isn't just about individual keys, though. It's about the entire wallet infrastructure.
BIP32's non-hardened derivation, that crucial feature every serious wallet depends on, relies entirely on ECC's linear algebraic structure.
Kill ECC, and you don't just lose key security. You lose the architecture that makes modern wallet management practical.
Post-quantum cryptography (PQC) has been making serious progress. NIST standardized several post-quantum signature schemes, most notably ML-DSA (based on lattice assumptions).
But here's the catch: these new signature schemes don't play nice with the math that makes BIP32 work.
Lattice-based signatures pose two specific problems for HD wallets.
First, many of them round their public keys to reduce size, which destroys the linear structure you need for non-hardened derivation.
Second, the secret key distributions don't behave predictably when you start adding things together, which is exactly what derivation requires.
So you're stuck in a bind. You can switch to quantum-safe signatures, but you lose watch-only wallets and the entire non-hardened derivation flow. Or you keep your nice wallet UX and pray that quantum computers take their sweet time. Not exactly a great set of options.
Construction one: The NIST-compliant option
The first construction uses ML-DSA, the lattice-based signature scheme that NIST has already standardized. If you're building something that needs to tick regulatory boxes, this is your horse.
The ML-DSA wallet supports hardened derivation, meaning you can still derive child keys from a parent private key, maintain unlinkability between keys (so nobody can tell two addresses belong to the same wallet), and achieve provable unforgeability (so nobody can fake your signatures).
The limitation, however, is that there is no non-hardened derivation. ML-DSA's public keys are rounded, which breaks the linearity you need.
So you lose watch-only wallets and the ability to generate fresh addresses from just a public key. For some use cases, that's fine. For others, it's a dealbreaker.
You could picture it like upgrading your house's locks to something quantum-proof, but losing the ability to give your neighbour a spare key that only opens the mailbox. The house is secure, but you've lost some convenience.
Construction two: The real breakthrough
The second construction is where things get genuinely interesting. It uses Raccoon-G, a variant of the Raccoon signature scheme that uses Gaussian-distributed secrets.
Here's why Raccoon-G works where other lattice-based schemes don't. Remember those two problems, rounded public keys and unpredictable secret distributions? Raccoon-G addresses both.
First, the team modified Raccoon-G to publish full, unrounded public keys. This preserves the linear structure needed for child key derivation.
You can still add things to a public key and get another valid public key, just like with ECC, but now on a lattice-based foundation.
Secondly, and this is the elegant bit, Gaussian distributions have a beautiful mathematical property: the sum of two Gaussians is another Gaussian with a predictable, slightly wider variance.
So when you derive a child key by adding randomness to a parent key, the child's secret distribution is still Gaussian.
It's a bit wider, sure, but it's statistically indistinguishable from a freshly generated key, so no attacker can tell the difference.
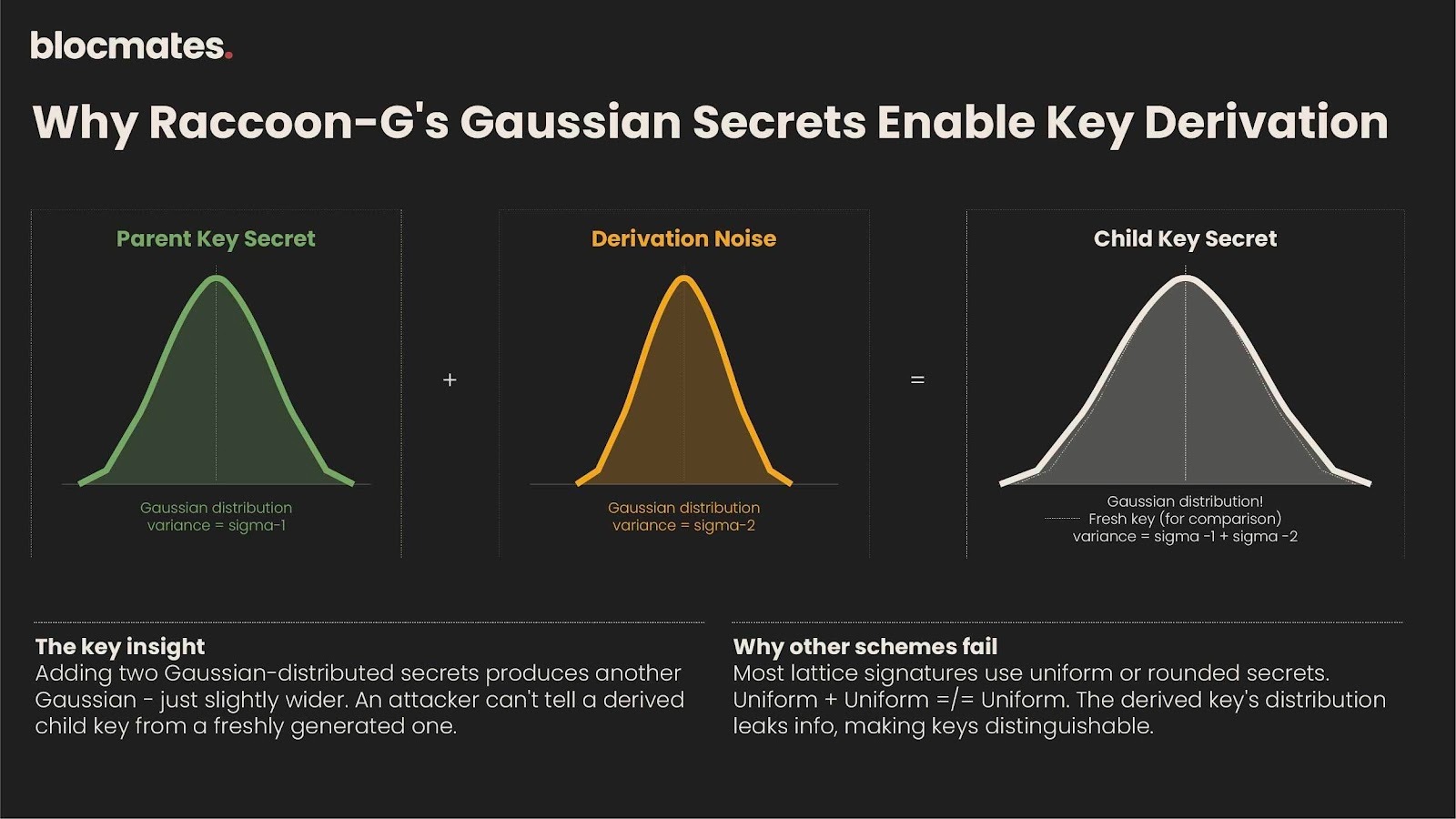
It's like mixing two cups of slightly different-temperature water. The result is still water, just at a slightly different temperature that nobody could distinguish from a fresh pour.
This means the Raccoon-G construction recovers BIP32's full non-hardened derivation. Watch-only wallets work.
Servers can generate addresses without private keys. The whole workflow that wallet developers and users depend on survives the transition to post-quantum crypto.
The security proofs are grounded in standard lattice assumptions - specifically Module Learning With Errors (MLWE) and Module Short Integer Solution (MSIS). No exotic assumptions or complex auxiliary machinery needed.
The tradeoff that won't go away
Here's the tension the paper openly acknowledges: Raccoon-G is not on a NIST standardization track.
It was part of the broader Raccoon signature effort, but it isn't going through the formal standardization process.
So you've got two paths. The ML-DSA wallet gives you compliance and standardization, but limits you to hardened derivation.
The Raccoon-G wallet gives you the full BIP32 feature set but relies on a non-standardized scheme.
For protocols and institutions that need to check regulatory boxes, construction one is the pragmatic choice. For the broader crypto ecosystem that needs practical wallet infrastructure, construction two is where the real value lies.
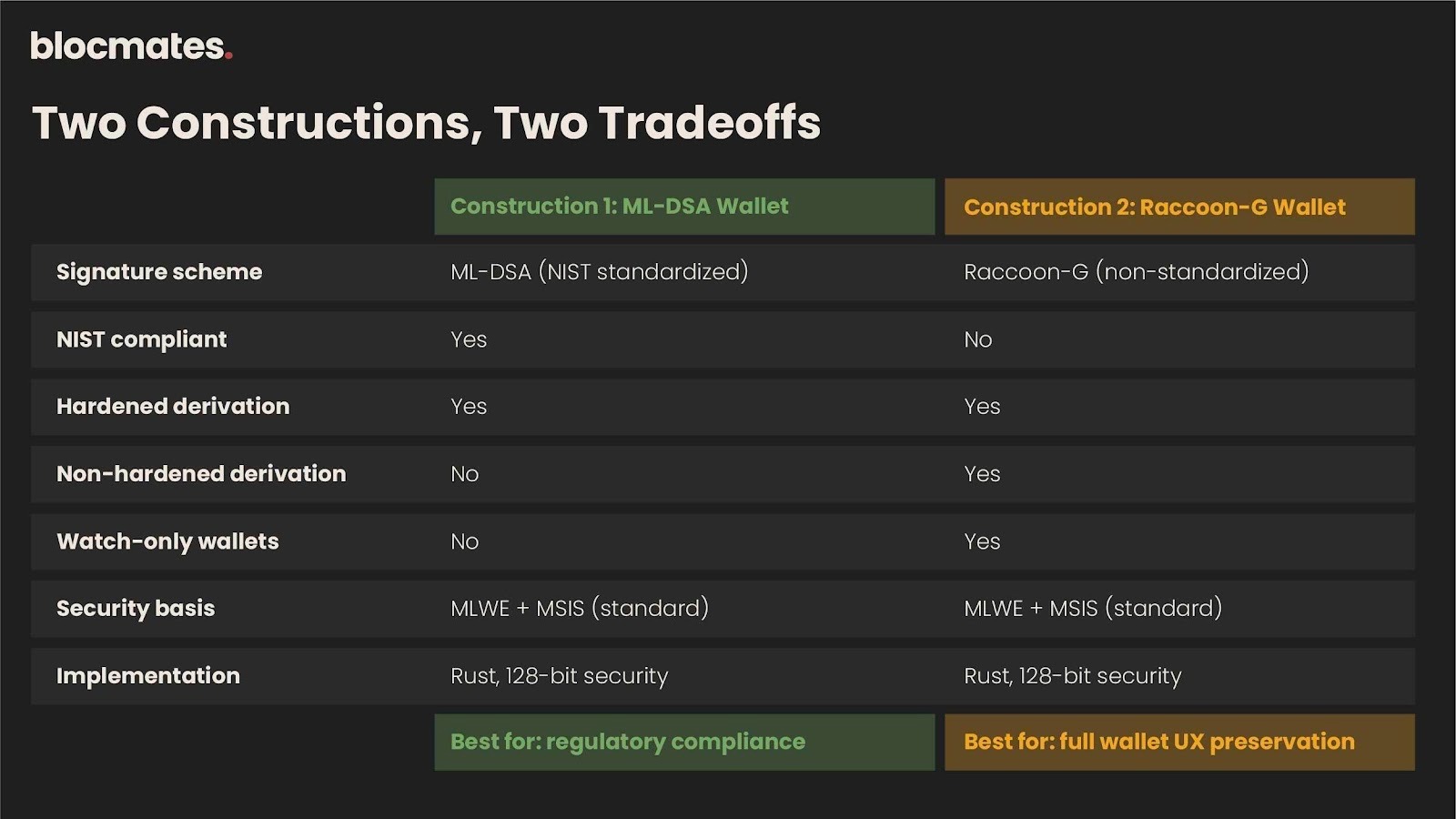
Both constructions are implemented in Rust and target 128 bits of security, consistent with BIP32. The source code is open and available on GitHub.
It's labelled as proof-of-concept, unaudited, unoptimized, and not production-ready, but the fact that it exists as working code rather than just equations on paper is notable.
Why this matters right now
Project Eleven has been building toward this moment for a while. They raised a $6 million seed round in June 2025, followed by a $20 million Series A in January 2026, led by Castle Island Ventures with participation from Coinbase Ventures, Fin Capital, Variant, and others, valuing the company at $120 million.
They've shipped YellowPages, a tool that lets Bitcoin (BTC) holders generate quantum-resistant keys and bind them to existing addresses without moving coins.
They launched the Q-Day Prize, offering 1 BTC to anyone who can crack an ECC key using Shor's algorithm on a quantum computer.
They've built the first post-quantum testnet for Solana. And now they're tackling the wallet infrastructure layer with peer-reviewed cryptographic research.
The lattice HD wallet paper isn't just an academic exercise. It's a piece of the migration puzzle.
If the crypto industry is going to transition from ECC to post-quantum cryptography without breaking the user experience, someone needs to figure out how to keep HD wallets working.
Project Eleven just published the first construction that does it with provable security under standard assumptions.
The bull case
Post-quantum cryptography is moving from theoretical concern to active infrastructure priority.
The White House published a crypto policy roadmap in 2025 that explicitly flagged quantum threats and called for proactive migration.
NIST is phasing out quantum-vulnerable algorithms. Resource estimates for running Shor's algorithm have dropped by a factor of 20 in the last year alone.
Project Eleven is positioning itself as the company that bridges research and deployment for this transition.
They're publishing papers, shipping tools, building testnets, and working directly with protocols like the Solana Foundation on migration planning.
The lattice HD wallet paper adds another piece to their moat - deep, original cryptographic research that solves problems no one else has (yet).
The bear case
Raccoon-G isn't standardized, and standards matter. If NIST or another body doesn't eventually bless a signature scheme that supports non-hardened derivation, the industry might have to accept a degraded wallet UX or wait for new standardization rounds.
That could take years.
Quantum computing timelines remain deeply uncertain. Blockstream CEO Adam Back has argued that BTC's encryption should hold until around 2035.
If the threat is further out than Project Eleven's positioning implies, the urgency (and commercial opportunity) diminishes.
And there's always the governance problem. Bitcoin takes years to upgrade by design.
Even if the cryptographic solutions exist, getting consensus to implement them across the network is a whole other challenge.
Project Eleven's yellowpages approach sidesteps this by working offchain, but the full HD wallet migration would eventually need protocol-level changes.
Concluding thoughts
Project Eleven's lattice HD wallet paper is a genuinely important piece of research.
It's the first time anyone has built a post-quantum wallet construction that recovers the full BIP32 feature set - non-hardened derivation included, with formal security proofs under standard assumptions.
Is quantum computing going to break Bitcoin tomorrow? No. Is the migration going to be painful when it happens? Absolutely.
The teams doing the hard cryptographic work now, before the deadline, are the ones that matter. Project Eleven is doing that work.
Your 12 words are safe for now. But the math underneath them has an expiry date, and someone needs to build the replacement before the clock runs out.














.webp)

.webp)
.webp)



.webp)
.webp)



.webp)

.webp)





















.webp)

.webp)
.webp)

%20(1).webp)























.webp)
.webp)

.webp)
.webp)
.webp)


.webp)
.webp)










.webp)


.webp)








.webp)







.webp)



.webp)






















.webp)






.webp)














.webp)

.webp)
.webp)

.webp)












.webp)
.webp)


.webp)







.webp)




